PRE2015 3 Groep1
Group members
- Indy Hoeks - 0911750
- Aaron Steinbusch - 0903892
- Valery Visser - 0847109
- Goos Wetzer - 0902160
- Viktor van Wijk - 0905890
- René Zaal - 0810911
Introduction
In the Netherlands, about 100 million every year is spend in the construction industry on vandalism and criminality. Companies are bankrupted by the thefts occurring on building sites. To prevent these thefts, nowadays building corporations install stationary cameras. Those cameras themselves are very expensive and their application is cost intensive. These cameras must be positioned multiple times, because of the changing building sites. Besides, there are mostly no walls or parts the cameras can be attached to. This results in very expensive camera units, which carry the cameras on poles, or solutions where stationary cameras must be repositioned multiple times. The solution given here is a drone, which covers the whole area, has significantly less blind spots, and delivers solutions for a better recognition of the intruders and retracing the stolen goods. In order to demonstrate the capabilities of a security drone, a simulation will be made. In this simulation, a break-in on a building site will be simulated while the building site uses one or more security drones as a security system.
A drone assisting security. It will able to detect suspicious activities in corners or difficult spots. These spots would be blind spots for regular surveillance cameras. Thereby the prejudice of flying security drones is, like already stated in the previous paragraph, that they can cover large buildings, with less cameras. The drone can notice suspicious movements and if it does, the drone can warn security. Which can there-after check whether there is actually something wrong. This can be done by looking at the footage the drone sends. In the meantime, the drone will follow the person or object that triggered the alarm, and record what it sees to help recognize the perpetrator, if he/she escapes. If a perpetrator takes the drone down the alarm will go off automatically. If drones are used as surveillance cameras or guards, less actual security guards will have to be hired. Therefore, the costs for the security will go down. Another prejudice is the fact the drone can be used if stationary cameras are not an option. For example on building sites where a lot of stuff is stolen or on open areas where it is simply impossible to mount a fixed camera.
The drone could also be used for secondary uses during the day: The company could use it to make pictures or videos. However, this will not be the aim of this project.
This page shows a new solution for building companies and security companies, with all properties of the system clearly and elaborately discussed and a recommendation for the changeable aspects of the drone.
Scenario
To show the importance of the system, there are two scenarios made. The first scenario directly corresponds to the main application of the proposed solution. The second scenario is another possible implementation of the system, which could be used in the future.
Tuesday 20th December of 2016
This year’s winter came late, very late. But now it's almost time for Christmas, the weather conditions finally act like winter came too. Last night the soil froze and small snowflakes started to fall. The building site will be totally abandoned for at least two weeks, because of the predicted snowfall and cold. All the gear will be left unattended. But not totally unattended. The security drone was introduced to the building site a week ago. Programmed to keep an eye on all places where the valuable gear is located it circled around all night to catch the intruding persons which tried to steal the specialized gear. And now, the drone will work for two full weeks. His first night has been done already. The cold environment made it actually easier to detect the warmer bodies of the intruders, and the alarm had gone once in the last night. The intruder was scared and fled right away. But while circling around the building site in the morning dew, a moving thing was detected with the heat sensors. Following it at an appropriate distance, a signal was sent to the security guard located at the central station. Even though the guard responded within a minute, the drone had trouble following the intruder, because of a combination of snow and fog. After continuing the direction the intruder went the intruder came in sight again and the drone started to follow the intruder after the signal of the security guard. Considering the person hadn’t reached the valuable goods yet, the goal was to scare him away. So the drone starts to make loud noises, shine a bright light at the intruder and tries to take pictures of the intruder. This intruder seemed to be careless, because he continued to run towards the valuable goods. While he gathers the stuff, the drone circles around the intruder and tries to make as many photo’s as possible, with the face if possible too. The police is already warned the moment the security guard accepted the signal of the drone about the intruder and is now on its way. Following the intruder the drone sends its location constantly to the guard at the main station. Therefore when the police arrives, they can locate the intruder as fast as possible. But the person starts to leave the building and heads towards another direction as they came from. The drone keeps following at a close distance, and sends the police its locations. The sirens of the police are already hearable and the intruder starts to run faster and faster. But it’s already pointless. The good communication between the system and the security makes sure the police is as effective as possible and the intruder is caught at the entrance it would take to exit the site. The pictures are used as evidence, to proof that the person was stealing. Otherwise it could be used in face recognition or in search warrants. The success of this drone is again proven. On to the next 13 days of 24 hours watch!
Friday 14th February 2020
A couple of weeks back, the Rijksmuseum in Amsterdam was the first large institution that implemented drones to guard the building. The decision to invest in flying cameras was made because of the increasing number of burglaries in museums around the capital city. Besides this, the costs of security guards were becoming higher and higher, and a change was needed. The patrolling security guards have been fully replaced by the flying cameras. These drones can photograph and film the environment, and chase a possible suspect. If they encounter something unusual (moving objects or a change in the environment) they send out a signal to the control room. The cause and severity of this unusual situation is then evaluated by a security guard in the control room.
On that particular evening, it is raining like it hasn’t rained in months. The newly installed drones are monitoring the hallways and exposition rooms as usual. After a couple of hours patrolling, one of the drones detects a small object that hasn’t been detected in previous rounds. The head of security is notified and looks at the footage sent from the robot. The object moved very fast and disappeared through a hole in the wall. Unless the Russians are experimenting with spying rodents, it is most likely an innocent rat. If the security guard wasn’t present for the determination of the threat, the drone would have activated the alarm for a rat, which is of course not desired behavior. After a couple more rounds, one of the drones detects a slightly opened door. It notifies the guard in the control room he has to start looking at the footage, while it moves closer to the door. Again, something small appears, but this time it stops moving in the middle of the hallway. Before the guard can determine what the object is, the screen turns black and the drone stops sending out its active-signal. It is at this point the guard knows the drone has been shut down, if not completely destroyed. He immediately sends another drone to the location and sees smoke and human-sized objects moving around it. The alarm is immediately sounded and the police is notified. Because of the smoke, it seems like the intruders haven’t noticed the second drone yet. This is why the guard commands the drone to follow them silently and stay at a distance. At one point, they are busy taking down some of the paintings and the drone finds a good moment to try and take pictures of the intruders’ faces. One of them quickly turns away his head, while the other one didn’t react as fast as his companion. Together with the face recognition system of the Dutch government, a name is quickly linked to this face. The drone then gets hit with an object and bumps into a wall. Because it is well protected against this violence, it is able to correct itself and gain some distance from the intruders. At this point, they know they have been spotted and decide to quickly leave the building. The drone follows them at a safe distance to the emergency exit, but has already locked it. They then smash a window and climb out of it. Normally, the drone will not follow suspects outside the building where it’s installed, but since the police has almost arrived, the guard commands the robot to follow them. As soon as they split up, the drone recognizes the clothes of the intruder it hasn’t photographed properly. It decides to follow him, since the other one is known already. Due to the GPS tracker in the drone, the police is able to follow him.
Focus
Requirements
The requirements are divided in functional and non-functional requirements, and analysed using the MoSCoW method: Must have requirements, Should have requirements, Could have requirements and Want to have requirements.
Functional
Must have
The drone must be able to fly, especially outdoors, in a changing environment. The building site changes a lot, so the drone must be suited for loads of different situations. The drone must also be able to fly its way through this building site. The drone must also be able to land safely on its own. De drone must be able to navigate through this building site to the hot spots indicated beforehand. By its navigation it must be able to find its docking station at the end of its shift or in case the battery is low. It must reach its docking station before the battery is completely empty. The drone must be able to communicate abnormalities to the guard and react at the guards decisions. Thereby the drone must never take actions it’s not allowed to without explicit permission of the guards or reject the guards decisions. Another communication aspect is the fact the drone must always confirm its location (coordinates e.g. by GPS) to the guards, and signal the guard if there occurs a defect in the drone. Defects can be a take down by for example an intruder, but also a broken propeller or suddenly empty battery. The drone must be able to detect intruders by an infrared camera and/or its movement sensor. The drone must be able to detect at least 99% of all intruders. After an intruder is detected and the guard has confirmed the intruder, the drone must be able to follow the intruder and take photos of the intruder. These photos must be send to the guard and saved somewhere there. The drone must film its restricted area.
Should have
The routes it takes should be random. This way, the drone is not predictable and therefore better applicable. Thereby it should even land safely if one of the propellers or motors shuts down. The drone should have nearly continuous streams of data feeds, to adjust its navigation in an optimal manner. Missing data or slowly arriving data could negatively influence navigation and the reaction of the drone. It should not be possible to hack the drone. The weight of the drone should be as less as possible to reduce the impact of accidentally occurring collisions by reducing the kinetic energy. But the drone must be able to withstand mediate/moderately strong weather forces, where some robustness and therefore weight is needed. The optimal balance between those two must be found. The drone should be as silent as possible, because otherwise possible intruders will hear the drone. The done should be undetectable by its sound for distances of 10 meter or more. The drone should be easy to use for the guard. Giving validation for actions must not take long and understanding the signal the drone sends must also be easy in order to react as fast as possible.
Could have
The more complicated a drone will be the more (technological) problems are given the possibility to intervene. Therefore the more complex the drone and its actions, the greater the decrease of its reliability. This is why it could be useful to keep a drone as simple as possible.
Want to have
The drone could be less visible, but its visibility possibly discourages intruders. Therefore this is not very important.
Not functional
Must have
The drone is meant to surveille a specific area, and therefore must never leave the intended area. This area is surrounded by fences, which are recognition points for the drone. It must never collide with objects or persons. It must also never intentionally harm or interfere directly with someone in the building. This would be prevented by signals received from sensors on the drone. The drone must in all cases be able to react to unexpected situations in a safe, harm avoiding way. It must never harm persons in unexpected situations. The lightning and simple transmission signals must not interfere with the navigation or communication of the drone. It is especially significant when the drone can’t be controlled or influenced in its decision making by external signals.
Should have
The drone should not film outside its restricted area. It should also not harm the privacy laws in a country. Therefore it must be clear that if you enter the restricted area, there is video recording present. This should be done with signs around the area that warn you that it is forbidden to enter the area as well as that there are drones with cameras in this area. In case the drone is following a suspect, it must not follow it outside the restricted area, because this would be filming in public domain and this is illegal. The drone should also be cost reducing for security companies and therefore for corporations. Otherwise the solution is not improving the situation and therefore not very beneficial.
Want to have
In case more drones are used together, they need to communicate with each other to cover the place and to prevent them of being at the same spot. This would be useless. One solution would be one main system, which decides what spot should be next to navigate to. This way it is still random, and the drones don’t interfere.
Stakeholders
Stakeholders have an interest in the development of a certain technology, but that does not necessarily mean that they can influence the development of the technology. These are some of the most important stakeholders regarding security drones: The first group of stakeholders are people that live close by an area that is being controlled by drones. These people might be inconvenienced by the noise the drone might make. On the other side, these people might feel more secure because these drones are patrolling an area close by. So, for these people, security drones will probably have both pros and cons. Security guards as we know them now are also important stakeholders because the security drone will partly replace regular security guards. These security guards would become unemployed because of this technology. So for security guards, introducing this technology will have unpleasant consequences. Another stakeholder would be an insurance company. Less break ins and especially less unsolved break-ins will lead to a more optimal situation for the insurance companies. Furthermore any footage of the drones can clear situations which involve fraud by employees or anything. These will all be caught on tape when the drone is working. This shows that introducing security drones will be very beneficial for insurance companies.
Users and their needs
Primary
There are a lot of users profiting from this system. This system will, as already mentioned, be used as addition to the security of a site. The primary user of this system will be the security manager, which is located in a control room and responding to all alarms or messages the drones will send. This control room could either be in the building itself, like museums or military buildings which need extreme surveillance, and where it is essentially to react within seconds on site. Or this control room could be in a strategic place, and be able to manage multiple buildings or sites at the same time. Either way, the security is the primary user of this system, because he interacts directly with it, and is the person responding to it. Those primary users will think the system is useful because it gives warnings at detected movements or displacements. The system will detect more small changes than a person could, and therefore help the security manager to make less mistakes, or overlooked clues.
The security guards need the drone to be easy to use. The drone must be able to give a clear view of the area where movement is detected in order make sure that the security guard with overview can make proper decisions. The guard also needs to be trained in how to work with these machines so they know the skills and limitations. For the specific implementation of the drones, lots of tests needs to be done such as how many drones can be monitored by one guard, and what are the tools the drones can use to stop the burglar without doing harm.
Another primary user will the be intruder. However, the drone will probably have little to no real interaction with the suspect. It could be possible for the drone to let the suspect know that he is being detected and that the police is on its way, but you cannot expect the drone to “arrest” the suspect, or to order the suspect to stop trying to escape. In our society, people simply would not let themselves be arrested by a machine or robot, because it is not a human. Moreover, since the drone does not have access to any type of violence or threats, it is very difficult to force an intruder to leave the stolen things and kindly wait for the police to arrive.
Secondary
The secondary users are the security companies. Because their security managers make less mistakes, they function better and will provide better surveillance. Furthermore the system will be less expensive. Therefore, less manpower is needed this way and there will be less installation costs, because you don’t have to install and implement more complicated systems like hidden cameras. Another secondary user is the company or owner which hires the services of a security company using those drones. They will profit greatly by better surveillance, because of the previous named reasons. Even if the burglars succeed to break in, the drone will try to take pictures of the suspects, and to lock them in. By these pictures the persons will be tracked down sooner and this will be an amiable aspect of the drone for everyone.
The most obvious benefit for the companies is the decrease in security costs: Once the system is up and running they will need significantly less employees. The second benefit is the quality improvement of the security. Chances that burglars are detected are higher and because of that the amount of stolen goods will decrease. The last and very important benefit is the improving of the safety of the employees. They will not come in contact with the burglars anymore and that is a very important for the image of that company. More museums and contractors will hire drone security companies as a result of that.
Tertiary
A tertiary user will be the society. By helping to induce thefts and insurance costs. Other tertiary users will be the insurance companies. Less break ins and especially less unsolved break-ins will lead to a more optimal situation for the insurance companies. Furthermore any footage of the drones can clear situations which involve fraud by employees or anything. These will all be caught on tape when the drone is working. The last tertiary user will be the police and or the state. Those will profit especially from the pictures the drone takes from burglars. Those will be very helpful for the police in catching the guys and completing the investigation. The society will have an emerged scene of safety when they are in a private controlled area. Finally, if the companies have reduced costs for the security of their wares, they can decrease the selling price or increase the quality of their product. Once again this will be favorable for the society.
Technical Aspects
State of the art - types of drones [1] [2]
Needless to say, the different types of UAVs can be implemented using different technologies. A drone is a type of Unmanned Aerial Vehicle (UAV). As the name implies, it is a vehicle that can operate in the air, without any person operating it in the vehicle itself. There are two types of UAVs: Remotely Piloted Vehicles (RPVs): these are UAVs that are remotely controlled by its operator from a distance. Because of this, the person who controls the airplane makes the decision how the vehicle behaves. On the other hand, there is the drone. It is an unmanned vehicle that operates almost completely autonomous; The drone gets a target from a controller, and then performs the actions completely autonomously.
Micro- and mini-UAVs
These UAVs are the smallest type of them all. They can only fly up to a maximum of 300 metres and are about the size of an average adult hand. Because they are so small, they can manoeuvre in smaller and more complex areas than all the other types of UAVs. These are especially designed for urban environments and housings.
Tactical UAVs
These fly up to a height of between 3 kilometres and 8 kilometres and can communicate and be operated over a distance of 3000 kilometres and can function for a maximum period of 40 hours. These type of UAVs are used by military force, and can even be equipped with missiles.
Strategic UAV
These can fly up to a maximum of 20 kilometers, have a flight period of about 30 hours. These type of drones are also used by military force.
Floaters
The main piece of technology consists of the equipped camera and the rest is just a balloon with some propellers to keep or place it in position. Except for the camera, this type of drone has not advanced much in the past decades. Due to the balloon based concept, these drones are stable, inexpensive, inaudible, energy efficient, durable, can cover huge tracts of land, but must be tethered and sometimes be reeled in when stronger winds occur.
Planes
These are the most used type of drones in governmental and military parties. For example, the MQ-9 Reaper keeps the borders of the UK in check. As far as half a century ago, the military used drones of this kind for reconnaissance. Nowadays, the kinds of drones we are looking for when it comes to surveying large areas, are of the plane persuasion. These planes fly at several kilometers high and have special cameras on board for making sharp, detailed images from a large distance. They are suited for patrolling large areas (they are even deployed for forests and national borders) and can chase targets through open areas. They will however quickly lose a target inside a building since they are not able to turn quickly enough to navigate inside buildings.
Quadcopters and octocopters
There is but a small difference between the two, octocopters are a bit more stable and are more redundant, most octocopters can land safely when one of the propellers breaks. These types of drones have ruled the consumer market lately and are rapidly becoming more affordable. These drones are often incapable of flying very high or fast, but are exceptionally suited for usage inside buildings. Because they are airborne, they can easily navigate stairs and blockages that would stem most other robots in their navigation. Their ability to change direction quickly and make precise movements is helpful in quickly and safely navigating the corridors of a building. These type of drones are obviously the best choice for indoor surveillance.
State of the art - sound
The drone use must be as silent as possible, otherwise you can hear it approaching. While the technology for drones is rapidly evolving, physics demands certain limits in their use. One of the things that determines the efficiency of a patrolling drone is the sound it produces. After all, if a perpetrator does not hear the drone, the chance that he/she gets caught increases drastically. While the possibilities for indoor drones are limited in type and size, for outdoor applications such as industrial sites and estates the possibilities are unbounded. The general rule is: the bigger the propellers, the lower the tonal distribution. Often the sound pressure produced is similar if not the same, but at lower tones in the sound spectrum, the noise quickly becomes inaudible at a reasonable distance. For inside applications the most quiet applications are balloon based, but those solutions are not quick enough for keeping track of a perpetrator. This means that the largest possible quadro- or octocopter becomes the design for indoors. Since there are no size constraints for outdoors, the easiest solution available is having a large durable drone patrolling high in the sky.
State of the art - Equipment
Some equipment for the drone is required in order to detect intruders. The first equipment that comes to mind when detection motion is required is using motion sensors. These sensors are however not suitable for security drones because they cannot function properly when they are moving. One way to use these detectors is to only scan the environment when the drone is hovering. But this would significantly limit the capital gain of security drones compared to the standard security systems as they are now. An alternative is using thermal cameras. Humans and animals will light up on the recordings of a thermal camera due to their body heat. There is software available that can recognize and analyse this heat, which allows the security guard to receive a warning when a certain heat level is detected. An example of such software is FLIR Tools.
The security drones should also be able to make recordings which allow for identification of persons. This means it has to be a camera with sufficient quality. Thermal cameras alone do not seem to be very useful for identification. This means a second camera is required for identification. But there is also a third option: A two in one camera. This is a camera that has both a thermal camera and a regular camera. A camera that would be very useful for this application is the Mini Dual-Sensor Camera Module for UAV/UGV Integration. This dual camera has a FLIR TAU 2 320x240 pixel or 640x480 pixel thermal camera and a SONY 10X Optical Zoom 530TV Line Color Camera (w/12X Digital Zoom) regular camera and it is designed for drones. [3] The thermal camera also works with the FLIR Tools software mentioned above.
The Mini Dual-Sensor Camera has all the functions that the security drones need and it allows for detecting people while moving, while regular motion sensors do not have this ability. This is why this camera has been chosen to be used on the security drones.
Technical aspects to develop
Furthermore a drone is needed, which has the capability of switching its batteries and has a distance sensor for its navigation. Furthermore the drone needs GPS to know its location. The battery of a drone only lasts for a maximum of 45 minutes. Therefore it is useful to use a drone which can switch batteries. A system like explained in appendix A must be designed to establish this. This also means the drone must be either custom made or has the possibility of being adapted. Therefore the costs of the drone are quite high in the cost analysis. By combining these aspects and the same software the simulation uses, the drone can be finished.
Decision making
Decision making is an important part of the security drone. The drones have to autonomously decide what they should do in a certain situation. This decision is a complex operation for a drone.
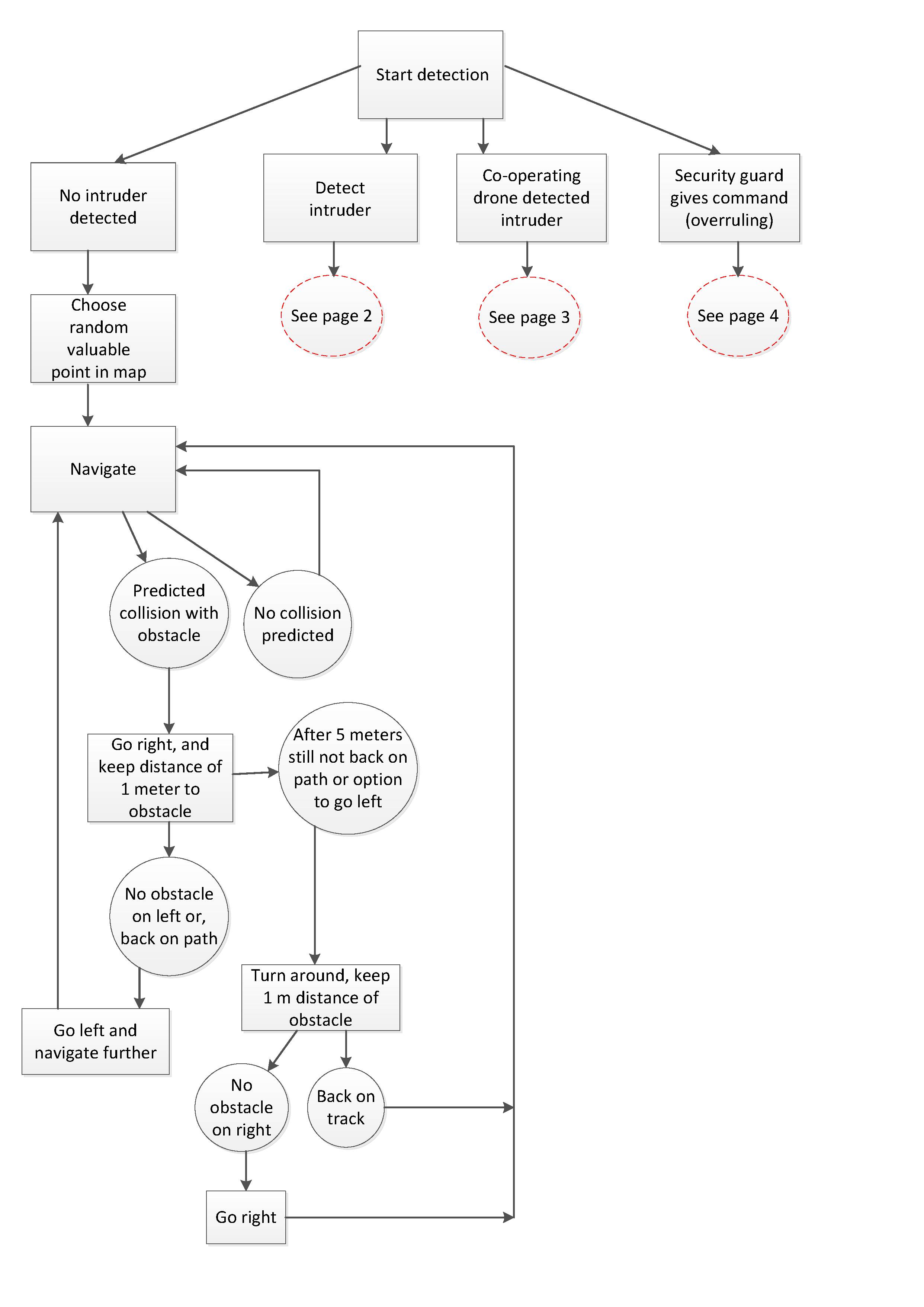
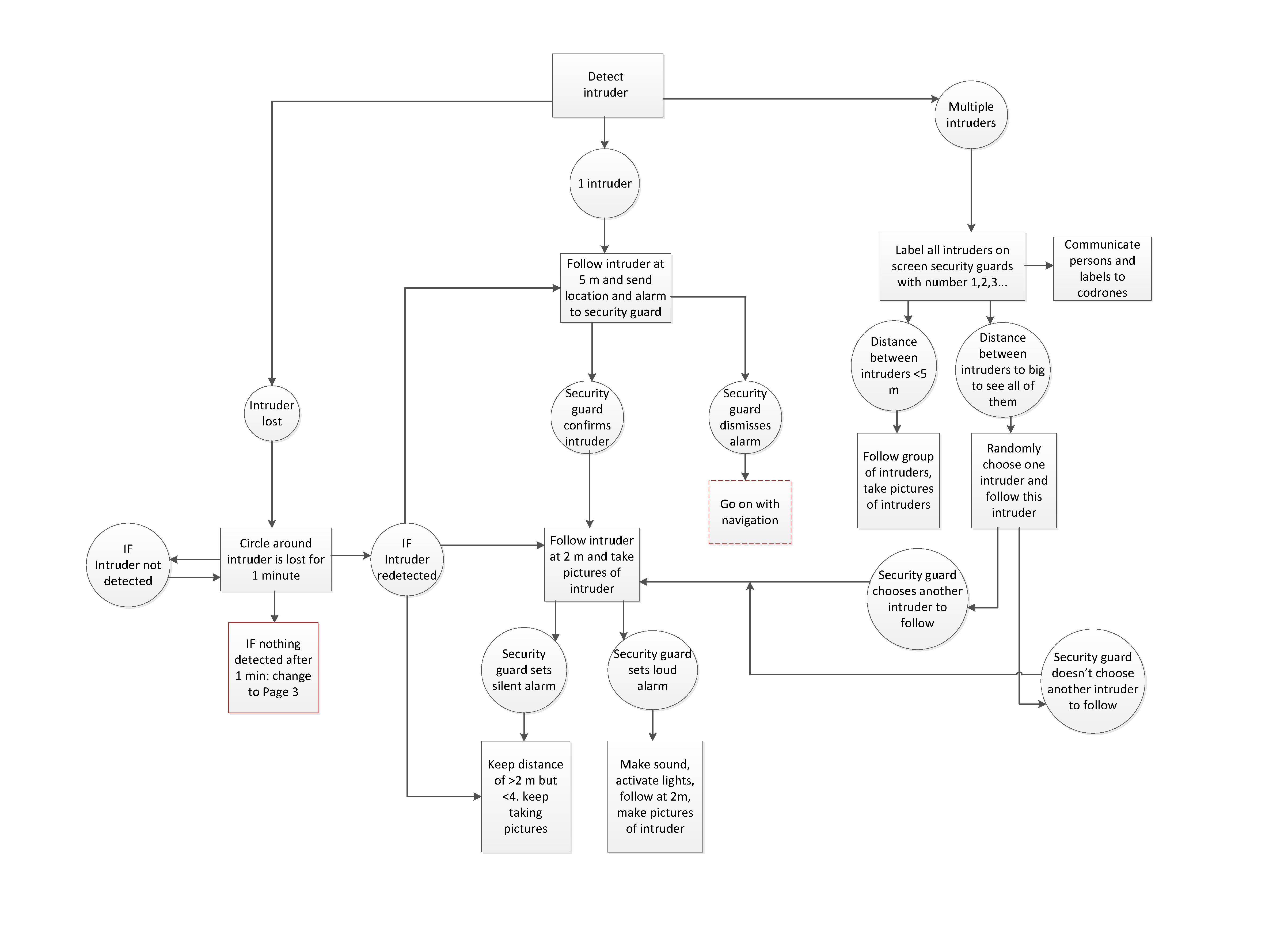
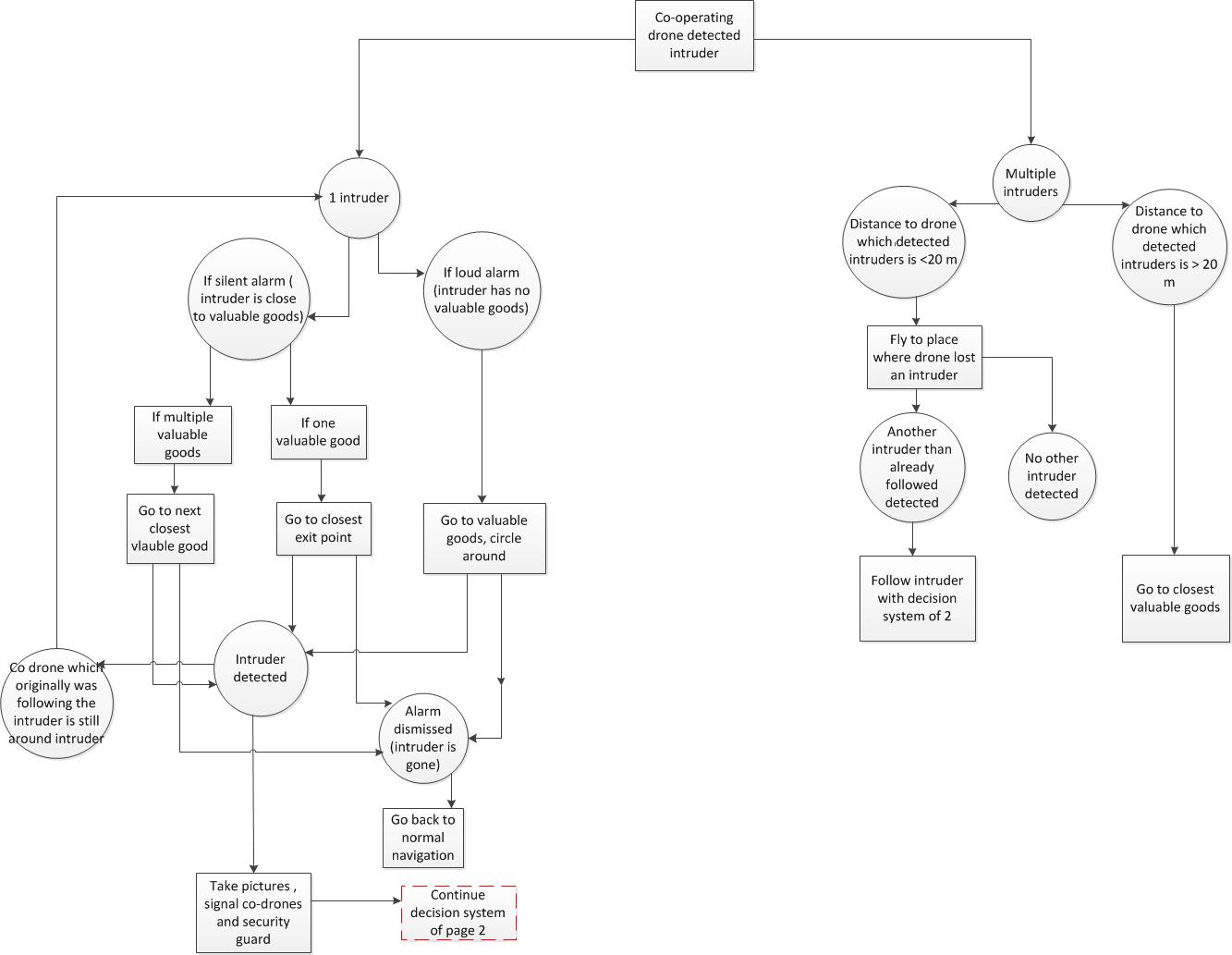
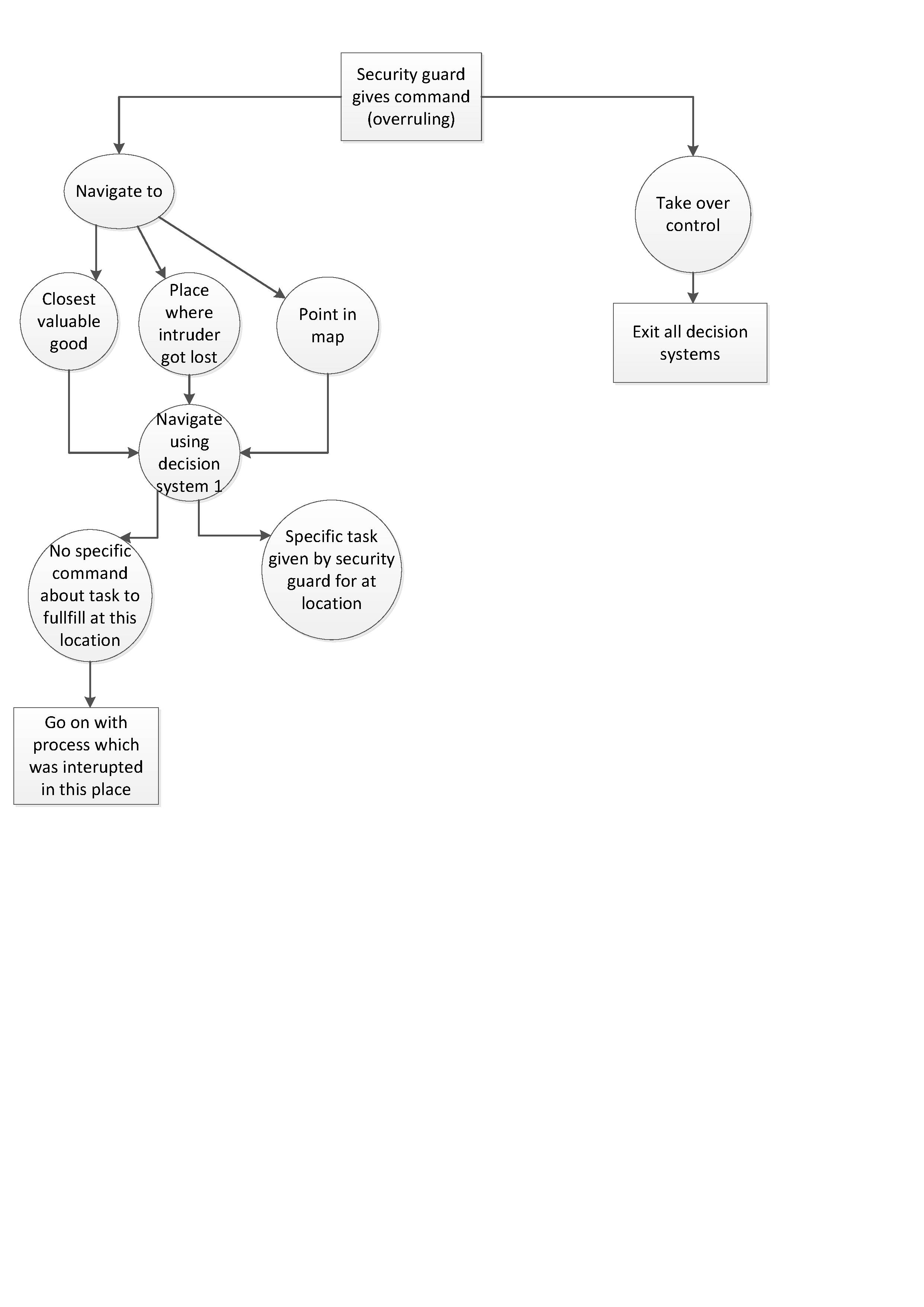
This section contains of three subsections. In the first section, a simplistic view on the decision making is given to get a general idea of what the possibilities are and what should be taken into account. In "detailed decision making", these things are further elaborated to get an idea of the in depth side of the decision making. With this information and knowledge, a decision making flowchart has been made which describes the decision making process as discrete and complete as possible.
Note that, the more drones you use, the easier it will get for drones to make a decision, because you do not have to choose between actions, each drone could do a different action. Autonomous decisions can always be overruled by a command given by a human.
General decision making
First of all, what could and should the drone do once it detects something? Even before the guard has decided whether this is a false alarm, or a legit alarm, the drone can be programmed to follow whatever it detected. This way, the guard can have a better look at what the drone detected and make a faster decision about the detection. It is important that the drone keeps a safe distance to the suspect while following because of the safety of the suspect. The guard could inform the drone to get closer to the suspect at some point if necessary.
Who to follow?
- One intruder:
The drone will autonomously follow the suspect and make pictures when it does, in order to identify the suspect. It does not need any further information from the security guard to know that it has to do this. This is quite an easy example with only 1 suspect.
- Multiple intruders:
What are the options when there's multiple intruders? Of course, a single drone can only follow one person at a time. So if multiple intruders decide to split up, it has to choose. It could choose to follow the first person that is detected, or the nearest person. These are examples of autonomous decisions, but the drone could also receive orders from the security manager, if he thinks it is better to follow another person.
Securing important locations
A whole different approach would be to not follow one of the persons, but to fly to some important location, for example a location where valuable goods is stored. One should consider that this strategy could help the intruder find valuable goods if they do not know where to look at first. A drone could also choose to keep an eye on the main or nearest exit.
Combining strategies with multiple drones
Using multiple drones would allow you to combine these strategies. And these strategies could all be pre-programmed into the drones, which means it would not require interaction between the security guard and the drones. But the security guard should still be able to overrule these strategies when he things this is necessary.
Losing sight of suspect:
Things would become more complicated if an intruder manages to somehow escape from the field of view of the drone. In that case the drone would not know what to do and it would need information from the security guard. The security guard knows how the environment looks and could predict what the intruder could do in a certain situation. So if an intruder chooses to hide under or in something, the security guard can inform the drone what to do, for example, if an intruder decides to hide in a trash can, the security guard will most likely tell the drone to just wait, because there is nowhere the intruder can go. The security guard could also choose to remotely control the drone himself because it would be too complicated for the drone to find the intruder again on its own.
Detailed decision making
Detecting multiple intruders
How does the drone decide who to follow in case of multiple intruders? It is very hard to instantly determine who you should follow in case of a break in, even for a human guard it is very hard to predict which of multiple intruders he should follow for a maximum result, which is minimizing damage/stolen goods and catch the intruders. For now, three options are listed in order to decide who to follow:
- Nearest person
- First detected person
- Random
Guard an important area
The drone could choose to fly and guard a specific area rather than following a suspect. This is a useful strategy if an area of building is being guarded by multiple drones. If one of these drones detects an intruder, the other drones could guard specific areas. This strategy can also be used in a situation where a single drone is being used and it loses the intruder. The intruder might run into the drone at one of these areas or scare the intruder away from important areas. These are the most important areas in most buildings and thus the best places for a drone to go to:
- Exits
- Locations with valuable goods
- Important connecting paths (some central point or hallway in an area)
Options in different situations
- In case of multiple drones, if drone 1 detects an intruder, drone 2 has not detected this intruder, so it does not know where this intruder is, which means the drone cannot follow that intruder. So the drone should do something else, for example guard a specific area.
- If the above happens, which area does drone 2 choose? It could autonomously always choose the closest point. (For this method there should be a list of locations for the drone to choose from).
- Choosing to secure valuable goods might not be the best strategy if the intruders already have taken some goods. At the moment of detection, the security guard decides whether he triggers a silent alarm (already stuff stolen) or a loud alarm (nothing yet stolen). The drone can use this information to predict where the intruders will go. If there is a silent alarm, intruders will probably search for more goods which can be stolen, so the drone should head to locations with valuable goods. But if there is a loud alarm going off, the intruders will probably try to escape so it is better to go to an exit in this case.
- It could also be the case that the nearest point for drone 2 (which has not detected anyone) is on the other side of the secured territory compared to where the intruder is detected. In this case, it might not be very useful to secure that nearest point. The drone could use the location of drone 1 (which is following the intruder) to have a rough location of the intruder. With this information, the drone could also choose to head to a point that is close to the intruder. (A bit tricky, what if this would take too long? → distance limit? )
- It could be an option to pre-program routes for drone 2 which it should fly when an intruder is detected. This way, the intruder could be intercepted. The route that it chooses to fly should depend on the location of the intruder (which is based on the location of drone 1), the kind of alarm that is going off (which can help predict where the intruder will go) and the area drone 2 is at.
Flowcharts decision making
In order to visualize the decision making and make it as concrete as possible, flowcharts are made that display the steps drones would run through to determine what the drones should do.
Ethical and Political aspects
Ethical aspects
If a drone happens to be in a situation where he can perform multiple actions with each having different outcomes, it should always choose the best outcome. This outcome should not be based on the performance of the drone (keeping the area as protected as possible) but also the most ethical one. Otherwise the drone could just lethally harm an intruder in order to protect the area, which is unethical. Therefore a form of ethics should also be implemented in the drone if it wants to be deployed in real life situations. If the drone does not contain this ethical system, then it can harm people and it becomes difficult to pin the one who is held responsible for the autonomic drone. So in order to implement this ethical system, we first need to look at the different kinds of ethical systems and how they apply to the drone. For this project, only two major forms of ethics were taken into consideration: utilitarianism, and Kantianism Utilitarianism is a form of ethics which can be summarized as the overall best outcome for the biggest group. If a drone gets into an ethical situation, it has to make a decision which makes the biggest group the happiest as possible.
However, a scenario of utilitarianism could be that the drone still lethally harms one intruder for the sake of an entire company, since the company will be the biggest and happiest group of people and only one person has to suffer. Kantianism thinks differently over this. Immanuel Kant (the inventor of Kantianism) formulated that a human being should never be treated as a means to an end. So as described above, beating the intruder for the sake of others is not an option according to Kantianism, since you use the intruder as a means to an end. According to Kant, the most important factor in determining what’s ethical is the concept of ‘motive’; that once actions is performed out of a ‘sense of duty’. For the drone, a duty could be that he should chase away the intruder on the construction site, if it tries to steal items. Of course, it still holds into account that he should harm the intruder to accomplish this as explained above. So the drone should chase the intruder away in a non-lethal manner, so no things such as Tasers, or pepper-spray since they can cause harm. One approach could be by scaring the intruder, this the drone could do by turning on lights or making noises, so that the intruder becomes aware of it and tries to flee. But there could be scenarios where the drone actually breaks an ethical rule. There is always a probability that this can occur, since a robot cannot perfectly be prepared for every possible scenario imaginable. So if a robot breaks an ethical rule, who should be held responsible for it? It could be held towards the engineers, because they are the once who designed and programmed the drone in the first place, so they are the one who also implemented the ethical system inside the drone. It could also be the company of the drone, since they are the one who green-lighted the concept, design and implementations of the robot. If they have given the robot a bottle of pepper spray to scare the intruder away, but ends up severely injuring the intruder for example, then they are the ones responsible for the injuries. A possible solution for this is that everyone should come to an overall agreement with the ethical behaviour the drone should and should not do. Companies as well as engineers as well as society should come to such agreement, so that the decisions made by the drone are overall the best possible decisions when looking at an overall aspect. It also depends on the unethical response of the drone. If it’s a programming error, than the engineers could be held responsible. If it’s a design error, the company could be held responsible and if it is an error made by the guard or intruder, then they should be held responsible. Of course a drone could learn from his ethical mistakes so that in the future, these mistakes are not made again. This form of implementation can be considered as artificial intelligence: an agent is capable of learning from its mistakes and its environment. If a mistake has been made, an agent could learn and adapt from his mistakes and also an engineer could give feedback towards the agent so that the agent learns from these mistakes and will perform better in the future. These learned actions for specific scenarios could also then be implemented in other agents to avoid the same mistakes again. Overall, if a drone happens to land in a scenario where he has to make an ethical decision, this decision has to be based on the best possible outcome for the biggest group possible without (lethally) harming anyone. And if the robot makes an unethical decision, the robot should learn from his mistake through the means of artificial intelligence and the once who should be held responsible should be based on the scenario, whether it’s a programming error by the engineers, a design error by the company or a personal error by the intruder or security guard.
Political aspects
UAVs can be equipped with many kinds of technologies, such as cameras, sensors, microphones and other communicating devices. Because these vehicles have these abilities, rules need to be made about what is appropriate and what not when using a certain type of drone. One of these themes for the rules is privacy. For example: in what type of situations can these drones be deployed in and what not? Depending on the drone's capabilities, which ways are appropriate or not appropriate to act on autonomously for the drone and its situation, it should also be clear who should be held responsible for the drones actions, if the drones acts in an inappropriate way.
Another example is from the Electronic Privacy Information Centre (EPIC). This party has called for federal agencies to regulate and control the proliferation of these machines that are used for purposes of surveillance; especially in the area of hacking drones and other UAVs. To protect drones from being hacked, EPIC came up with certain ideas such as to circumvent encryption codes within drone surveillance software and the ability to manipulate hardware to gain access to drone surveillance data.
All these types of rules and approaches should be made before any type of droid is officially released to the public. There should not only be certain rules that should hold for all different types of droids in general (like a droid should not do harm to anybody), but also specific rules for robots that have certain properties. Like for example: when a drone has a camera installed on it, it should not be able to publicly expose the footage it takes, because that would violate the aspect of someone’s privacy.
Needed expertises
As can be seen, some expertise is needed to establish the drone. To start there needs to be an expert in drone navigation to navigate the drone. It is expected that the drone can use a lot of the same software as the simulation uses. But still the drone needs to be assembled, and it has to be made ready to fly. Therefore, a drone specialist or drone mechanic is needed. The third expertise needed is a security guard to react at the drones signals. The rest of the drone is already created in the simulation.
Cost expectations
For this cost analysis a relatively simple model is used. The model consists of a square building site with some high unoverseeable objects. The model has a fence around the building site, to protect in the first case from intruders. The costs of the system depends of course on the duration of the system. For this analysis a time period of 1 month is used. The fee of a security guard is estimated around €16,- (night duty) and the fee for an installation engineer around €12,- per hour (both systematically hired, no self-employed guards). [4] In order get a better idea of the costs of systems that are being used today, three different situations are analysed.
Current market situation 1
For situation 1, a company that uses a security system was approached to gain insight of the costs for current security systems. The security system of this company consists of 6 cameras to oversee the area around the building. This building is 50 by 90 meters. The costs, including installation, are about €11.000,-. The cameras are €750,- each. So a total of €4500,- is spent on the cameras themselves. The cables for the cameras are very expensive, and building this network is time and cost expensive. This system is after installation integrated around the building and will stay there permanently.
What Costs Night vision cameras €4.500,- installation €6.500,- Total €11000,-
Current market situation 2
An example of cameras installed in a medium sized building site: "8 Cameras/Outside Motion Detectors/Loud Tannoy/Unlimited Out Of Hrs Monitoring £180 p/w." [5] This system has only 4 cameras and those are only night time cameras. Thus in weekends, the building site is still not fully protected. There is no security guard reviewing this system and the cameras are quite simple and have a small range. This way the building site is minimally secured. Therefore it is assumed, these simple systems are not a real competitor for the system.
What Costs Night vision cameras €920,- Contract with alarm receiving station €32,92 [6] Total €952,92
Current market situation 3
In the current situation, there are at least 5 stationary cameras needed. Night cameras which can see for at least 20 meters are around €750,-. The prejudice of these expensive cameras is they can see at day too. Those cameras are moved a lot and will be handled often. Therefore the prediction is that they will last for only a year. In one month €312,50 will be spend on these cameras. The installation costs are quite expensive too. Installation of a single camera is estimated on 30 minutes. Connecting the total in the main system would take at least an hour too. Furthermore, these cameras cannot fly. And a construction site does not have many objects to attach the cameras to. So another 30 minutes is required to make a construction of poles or something to attach the camera to. This would lead to a 6 hour installation procedure. The construction site changes continually. The corner cameras will be stationed all day long in the same spot. But the middle camera, needs to be moved about every week, to obtain optimal situations. Therefore every week 1 hour installation should be required for a secure situation. Every night a security guard is needed to control the cameras. A security guard works from about 10 o’clock in the evening to 5 in the morning. The construction builders start early so this is why the security guard is dismissed this early. But it is still a night of 7 hours with a fee of €30,- per hour. So this will cost €210,- per night, which makes €6300,- per month.
What Costs Night vision cameras €312,50 6 hour installation €72,- Security guard whole month €3360,- 1 hour installation every week €48,- Total €3542,50
Drone situation
The drone situation uses a thermal camera. These thermal cameras are quite costly. The estimation is about €2500,-. This would of course not be the cost reduction. But it replaces all 5 night vision cameras in the current building site. It has a normal camera too, with flash, so if an intruder must be captured, it will be able to do so. These cameras are made for outdoors and will only be handled by the drone. Because of their careful handling the expectation will be that they can last for at least 2 years of employment. Therefore they will cost 104,16 euros a month. A battery replacing system is included in the drone, because a drone's battery only lasts for about 45 minutes. Such batteries take about 1,5 hour to get fully loaded again, so the drone requires 3 batteries and the battery changing system. The total of the changing/charging system and batteries costs about 430 (3 times €105,- for the battery, €40,- for the docking system and €75,- for the system which plugs the batteries in and out). The batteries will last for about a year so €535,83 must be paid every month. The installation costs would be way cheaper. The docking station must be placed somewhere in the construction site and the main points to navigate to must be installed. This would only take 1 hour and no intermediate reinstallation in the whole period. Furthermore the security guard can overview 4 or 5 construction building sites in the same time. This would reduce the security costs to 1/5 of its original costs. The drone is an extra cost in this model. But the drone lasts longer than one month and can be reused. If the price of the drone is estimated on about €4000,-, and the drone is estimated to last for 3 years. In one month about €110,- must be reserved for the drone’s costs.
What Costs Thermal camera €104,16 6 hour installation €12,- Security guard whole month €672,- Drone €110,- Batteries €35,83 Total €933,99
Besides the material and fee costs, less intruders will be able to escape the security. Therefore there will also be a cost reduction in these things. This analysis presents a way cheaper and definitely more valuable detection versus the current situation.
Simulation
Definition
- The scenario that the drone will be tested in is a construction site.
- The scale of the site is 2000 m^2.
- The shape of the sites can differ.
- All construction sites are outdoors.
- The climate is that of a Temperate Maritime Climate (as in the Netherlands).
- The site is surrounded by a fence.
- Valuable materials are present on the site and there are a lot of obstacles and height differences.
Assumptions
The problem which is focused on is theft on building sites, when those are supposed to be abandoned. This means at night time or in weekends / vacations. These building suites are surrounded by fences, but still intruders try to break in quite often. The value of the goods located at those building sites are surprisingly high, especially the specialized tools. This is highly disadvantageous for the building companies. Therefore they try to protect their goods with the stationary cameras named before. But their reach and coverage is not enough to stop all intruders. Still there are valuable goods stolen because of mazes in the security of the building sites. Another problem is vandalism like graffiti on those building sites. Cleaning of this graffiti is expensive, especially when the constructions are new. The problem which must be solved is to cover the continuously changing building sites, to prevent theft or vandalism by intruders. Some assumptions have been made about the situations and the intruders.
- The intruders have breached the normal fences surrounding the building site, and will therefore always enter through these breaches in the fences.
- Except for intruders, no other persons or animals are able to enter the building site.
- The weather in the simulation is ignored. Therefore, the drone will not be influenced by wind for example.
- The simulation takes place at night
- The area is rectangular.
- When one of the intruders is filmed for three (or more) consecutive seconds, the drones 'win'
- When one of the intruders escapes with at least one treasure, the intruders 'win'
Intruder
In the simulation, there are a couple of moving objects. One of them is the intruder. Just like in the real world, this intruder is not supposed to be in a certain place, which in this case is the building site. Since the simulated situation is a break-in, this intruder is user controlled. To make the simulation as realistic as possible, it was decided to give the intruder some features a real-life perpetrator would have too:
- Running: besides walking, the intruder is also able to run. When detected by a drone, or if the break-in does not have to be stealth for example, the sprinting function can be used to get away quickly.
- Crouching: like running, crouching is also a way for intruders to sneak around a forbidden place. The crouching function in the simulation will also reduce the speed at which the intruder can move.
- Flashlight: since the simulated break-in will happen during the night, it would only be ‘fair’ to give the intruders a flashlight.
- Picking-up the valuable goods: the valuable goods can be picked-up and carried to the exit. This will cause the speed with which the intruder can travel to decrease, as if it takes effort to transport the item. These valuable goods can also be dropped again, if the intruder decides to run away without the loot.
- Hiding: besides crouching, it was decided to give the intruder another way of avoiding the drone’s detection. In the simulation, there is one kind of object in which the intruder can enter to hide from the drone: dixies. These objects are spread out over the area.
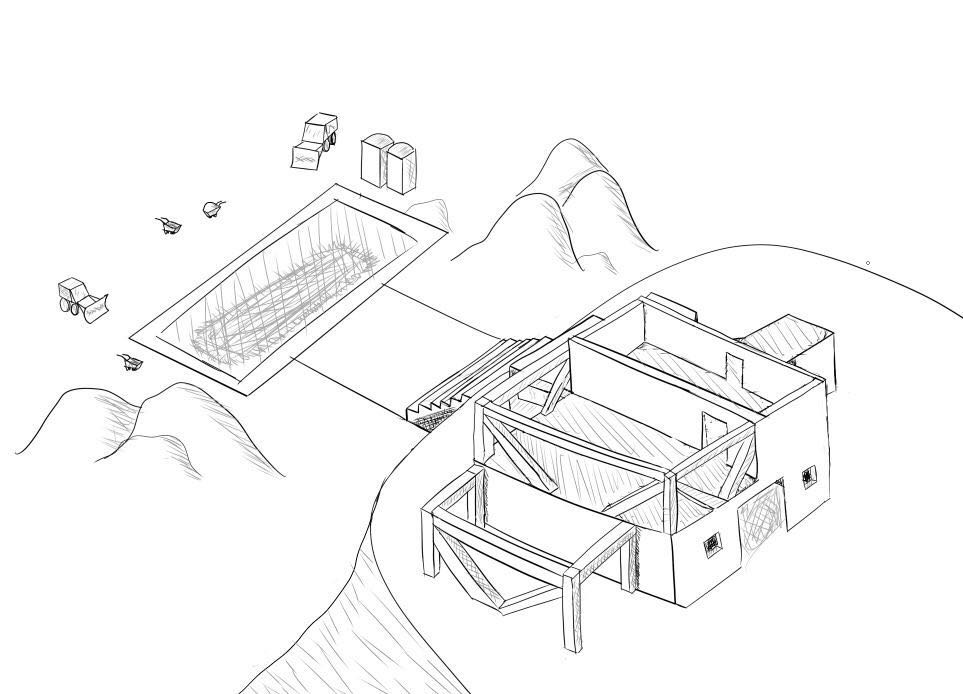
Scenario
In the near future, a guy who is filthy rich decided to build a mansion somewhere in the middle of nowhere with a swimming pool. Everyone around town knows that not only is this guy very rich, but also very lazy and clumsy, even so clumsy that he one day left his precious possessions somewhere around the building site of his new house. Some people heard about this news and decided to go as burglars to the construction site to find these priceless possessions and take them or themselves. However, the rich guy was prepared for the worst and in order to secure his area of construction. He implemented drones as security. The reason he chose for drones is because drones are vary applicable in his construction site, with the constantly changing environments of objects and building of the construction and he thinks that the drones are the future for securing areas.
Instruction Manual
The simulation that has been built makes the player play as the burglar. Their task is to search the area, finding the gold that the rich guy has left, pick up the gold and leave the area safely with it. If the perpetrators manage to succeed, they win the round. However, if they are spotted by the drone, then the perpetrators loose and the drones win.
In the environment, you can change the amount of drones you want to secure the area and also the amount of burglars that are in the scenario depend on the amount of players that participate in the simulation.
The following table shows a summary of the just-named move-set with to the right two additional columns that correspond to the primary and secondary key-bindings of the actions.
Action Key Binding 1 Key Binding 2 Move forward Up Arrow W Move backwards Down Arrow S Move right Right Arrow D Move left Left Arrow A Look around Move Mouse n.a. Jump Spacebar n.a. Crouch (hold down) Ctrl n.a. Sprint (hold down) Shift Scroll Wheel Pick up Left Mouse Button E Drop Right Mouse Button Q Interact with Dixies Left Mouse Button E Turn flashlight ON/OFF F n.a.
Considerations
Some concerns have to be made when implementing this system.
First of all the visibility of the drone. There are multiple pros and cons in making the drone easy detectable for everyone. First of all by making the drone visible, it may have a dissuasive effect. If it is thought the place is well protected, intruders or vandalists will be less inclined in entering the place. Especially those who commit minor violations like graffiti will watch out for those kinds of places. Especially because the drone with camera will be accompanied by clear informative signs on the fences which inform passer-by’s there is camera observation and security drones.
But in contrary the clearly visible drone will be easier to spot and therefore a person may be able to hide in time. Especially when the drone is also clearly audible, they can hide before being in their visual field. By that the drone is also easier to take down, because localization is easier. But if the drone is taken down, there will be automatically send to the guard. So in this situation the intruder will still be caught hopefully.
Another consideration is the interaction with the intruder. The drone can follow the suspect as silent as possible, so they will take their time to get everything and this buys the police some time to arrive. But the other possibility is to turn on a loud noise or lights, which scares off the intruder. The best possibility will be the combination. If the intruder is already with the valuable goods, the drone should stay silent for the police to arrive. But if the intruder hasn’t reached the valuable goods, and the loud sound goes off, this will probably scare off the intruder. Which hopefully leaves without taking anything. This won’t get the intruder caught, but it will prevent from theft.
Test Results
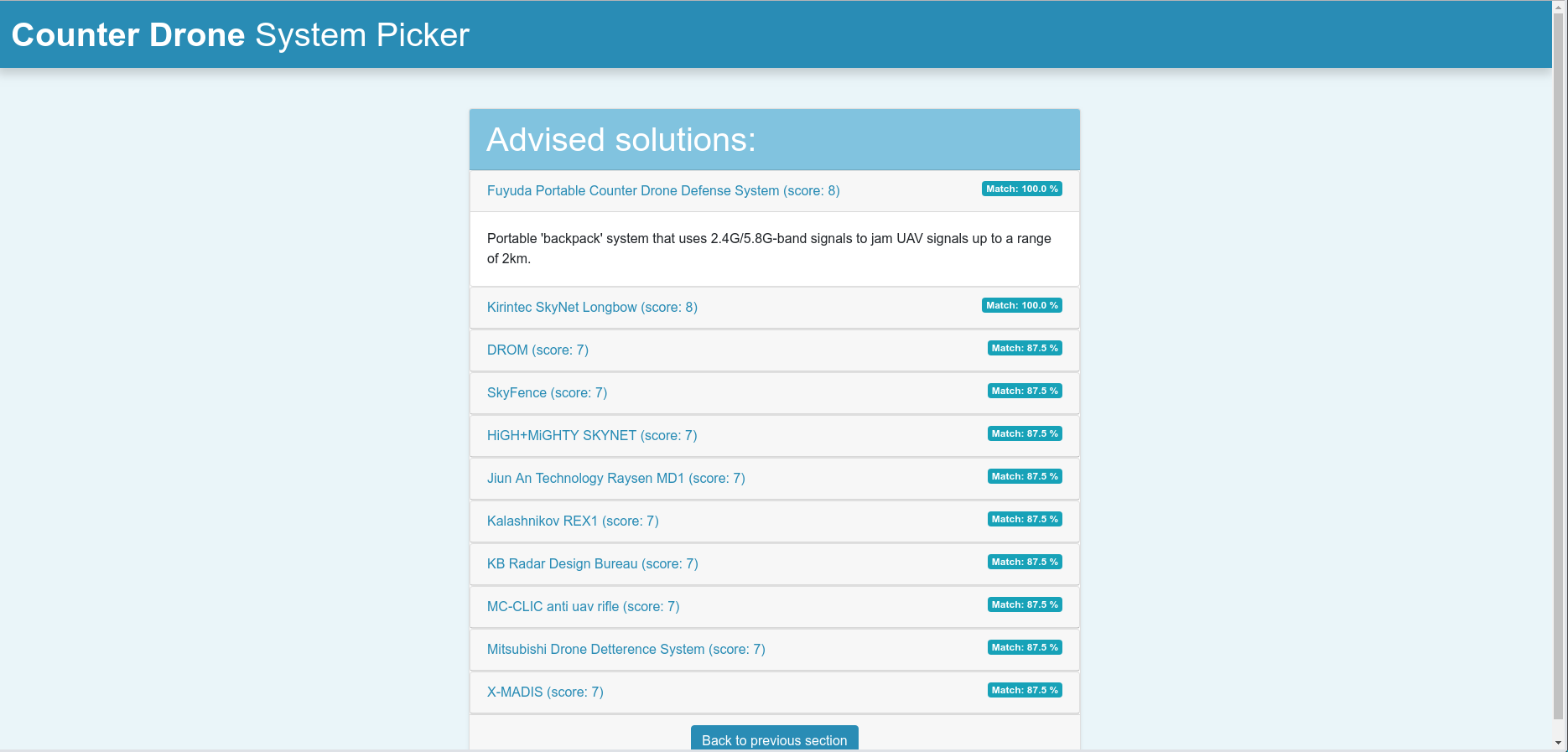
After the simulation had been finished, many tests were conducted to find out how well the area was secured in different settings. These settings depends on two things: the amount of drones securing the area and the amount of perpetrators entering the site. The minimum amount of drones and perpetrators was equal to one. The maximum amount of drones that have been used is equal to three and for the perpetrator, this was equal to two. This creates a domain of six different situations that were tested 10 times to create a probability of the drones successfully catching the perpetrators. The following graph shows the amount of catches by the drones in percentage.
Recommendations
These test results are not representative for all possible situations. If the construction for example changes, then the strategy of the perpetrators and the drone could change and thus could influence the test results if they were tested again in the new area. Therefore, these test results are not definitive, and should be used as guidelines. The catch rate depends on many factors: besides the amount of drones and perpetrators, it also depends on the size of the area, the objects inside this area, time of day, etc.
For a scenario that looks a lot like the simulation, than these test results could be used for recommendations. Which means the most recommendation would be to have two drones securing the area, if you look at the catch rate percentage and the total cost of the drones. If you buy three drones in this situation for example, you pay a lot more and still would get about the same results when using only two drones, thus making one drone unnecessary.
If these results would be used to recommend the amount of drones for different scenarios, then some variables need to be considered. An example of this would be how many square meter could the drone cover to obtain the same results as in the test? If the answer is based on the test results, to get the most optimal solution to answer this question, each drone should cover about 1000 square meter, since the simulation is about 2000 square meter and the most optimal situation to secure the area when also taking the costs into account would be two drones.
There are many things that can be taken into account that may have influence on the catch rate of the drones. Some of these can actually be overlooked, thus you can still hold a large amount of uncertainty when implementing the drones as security. To cover this problem, a recommendation of using one additional drone could solve this uncertainty for the greatest part. It could not cover the entire field of uncertainty, since that would be impossible.
Conclusion
The goal of this project was to show a new and better solution for protecting a certain area for building companies and to provide a recommendation at the end, so that the most optimal decision can be made for the company of interest. This solution is based on implementing drones as the main security and to show the pros and cons of this implementation.
At first, things that were taken into consideration were ethics and political aspects, the decision making of the drone and security guard, the users and their needs, the technical aspects and the costs.
Decision making was implemented for how the drone should act in certain situations. The ethical and political aspects were taken into account so that the drone would make better ethical decisions bedsides the decision making. The primary, secondary, and tertiary users were mentioned that needed to be taken into account for this project that also that included their needs that need to be considered.
A simulation has been built to make the recommendations, and the pros and cons of the implemented system. This simulation has been built simultaneously with this research so that this research could immediately be implemented in the simulation.
Discussion
Overall this was an exciting project to conduct. However, there were some obstacle that could be overall improved for future projects. Things such as the overall planning, especially the work distribution over the entire course, could be better. During the project, some things were not equally distributed, thus there were times where too many things had to be done according the planning. If the planning could be made such that all the tasks are more widely distributed, and that there’s room for a buffer in case things don’t go as planned.
This research did not take certain things into consideration, such as the weather inside the simulation. Things like these could be implemented in further research to make better considerations for example. Another aspect that should added to the simulation is about the interaction between the drone and the security guard. Besides the weather, things such as the size of the area, the amount of obstacles inside the area, different kinds of equipment on the drone, the height of the drone, and the height of the structures could also be experimented with to find different results and even improvements over this research.
Links
Planning
Week 1: (brainstorm)
- Introduction to the course
- Come up with ideas for the project
- Choose the best idea
- Make a first presentation
Week 2: (final idea)
- Literature research
- Process feedback
- Make a final idea presentation
Week 3: (research)
- Make a proper planning
- Research the considerations
- Safety (Valery)
- Privacy (Aaron)
- Decision making (Indy)
- Violence (Valery)
- Applicability indoors (Viktor)
- Derive requirements for the design
- Start with building the simulation engine (René)
Week 4: (start designing)
- Continue with the simulation engine (René)
- Environment design (Goos and Viktor)
- Improve requirements (Indy and Valery)
- Financial analyses (Valery)
- Research on motion detection (Aaron)
Week 5: (finish design)
- Continue with the simulation engine (René and Goos)
- Finish environment design (Indy and Viktor)
- Start with the business case: File:Business.pdf (Valery)
- Interaction/decision-making (Aaron)
- New sketch
Week 6: (testing)
- Finish simulation engine (René and Goos)
- Start implementing decision-making: File:Flowchartdrone.pdf (Valery and Aaron)
- Create intruders (Indy and Viktor)
- Business case V2: File:Businessv2.pdf
Week 7 (improving)
- Improve the design
- Document the process
Week 8: (documentation and finishing the wiki-page)
- Make multiplayer options (René)
- complete wiki-page with all work done(Valery)
- Write conclusions on research done (Valery)
- Write about all work done in unity (Indy and Viktor)
- Write ethics (Goos)
Week 9: (finishing the wiki-page)
- Put own written parts in wiki-page(ALL)
- Simulating (René)
- Spelling check (ALL)
Week 10: (Presentation)
- Make presentation
References
- ↑ Cavoukian, A. (2012). Privacy and drones: Unmanned aerial vehicles (pp. 1-30). Information and Privacy Commissioner of Ontario, Canada
- ↑ Haddal, C. C., & Gertler, J. (2010, July). Homeland security: Unmanned aerial vehicles and border surveillance. LIBRARY OF CONGRESS WASHINGTON DC CONGRESSIONAL RESEARCH SERVICE.
- ↑ OEM cameras, Product. Available from: <http://www.oemcameras.com/mini-dual-sensor-thermal-visible-camera-module.html> (22 march 2016).
- ↑ Uurtarieven in 50 beroepen: zzp'ers vergeleken met werknemers. Available from: <http://www.loonwijzer.nl/home/eigenbaaswijzer/tarief-check/uurtarieven-in-50-beroepen-zzpers-vergeleken-met-werknemers> (04 march 2016).
- ↑ Building Site CCTV, leading provider in Building/Demolition Site Security. Available from: <http://buildingsitecctv.com> (15 march 2016)
- ↑ SMC Alarmcentrale - Meldkamer Aansluiting. Available from: <https://www.credexalarmsystems.eu/nl/smc-alarmcentrale-meldkamer-pac.html> (12 march 2016).